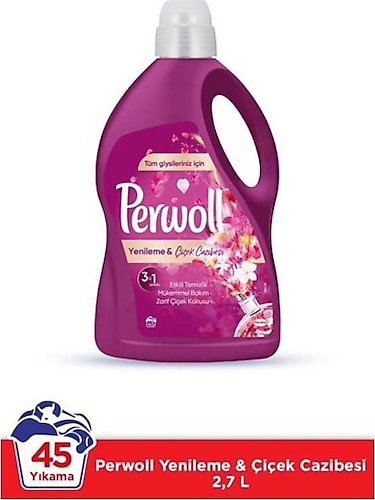
Perwoll Renk Koruma & Çiçek Kokulu Renkliler için Sıvı Deterjan 50 Yıkama 2.75 lt Fiyatları ve Modelleri - Pazarama

Perwoll Hassas Bakım Sıvı Çamaşır Deterjanı 4 x 3L (200 Yıkama) 2 Siyah + 2 Renkli Yenileme - OnuAl Fiyat Arşivi
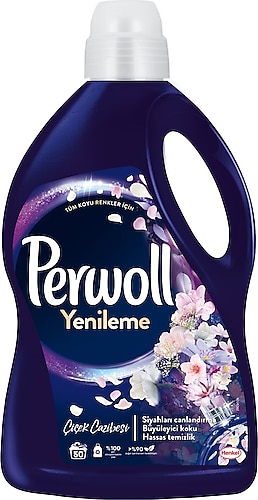
Perwoll Yenileme Çiçek Cazibesi Siyahlar için Sıvı Deterjan 50 Yıkama 2.75 lt Fiyatları, Özellikleri ve Yorumları | En Ucuzu Akakçe